In recent years, tokenization - the act of turning real-world assets or rights into digital tokens on a blockchain - has garnered significant attention. Powered by blockchain technology, artificial intelligence, and cryptocurrencies, this innovative method has transformed industries like finance, real estate, supply chain, among others. Nevertheless, as tokenization becomes more widely adopted, adhering to Anti-Money Laundering (AML) and Know Your Customer (KYC) regulations becomes increasingly important.
AML and KYC compliance within tokenization is imperative for tackling potential risks linked to financial crimes such as money laundering, terrorist financing, and fraud. Through the adoption of stringent compliance measures, businesses can showcase their dedication to upholding integrity, security, and transparency in the tokenization ecosystem.
This article delves into strategies and best practices for achieving AML and KYC compliance in tokenization. By abiding by these principles, companies active in the tokenization domain can protect their operations, stakeholders, and further solidify the industry's overall credibility and sustainability.
Understanding Tokenization and Its Regulatory Landscape
Tokenization
Tokenization, a procedure involving the transformation of tangible and intangible assets or rights into digital tokens on a blockchain, plays an essential role in various domains such as financial securities, real estate properties, intellectual property, and even tangible assets like art or collectibles. By harnessing the advantages of blockchain technology – immutability, transparency, and decentralization – tokenization offers a secure and efficient way to represent and transfer assets.
The regulatory environment of tokenization and adherence to AML and KYC regulations
With increasing adoption of tokenization, global regulatory bodies actively evaluate its ramifications and devise frameworks to mitigate potential risks and ensure compliance. The regulations concerning tokenization differ across jurisdictions – some embrace innovation while others enforce strict rules.
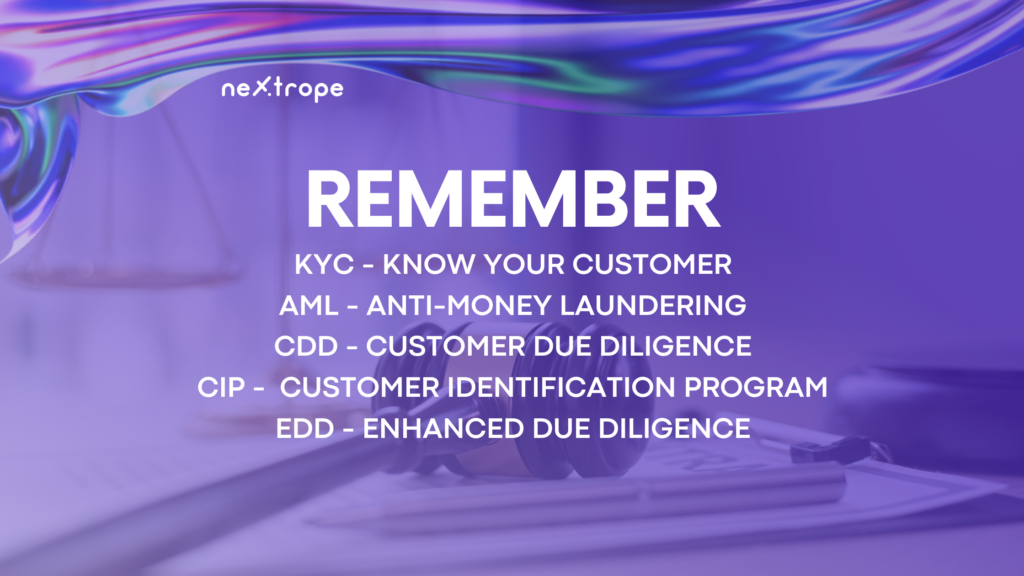
Adhering to Anti-Money Laundering (AML) and Know Your Customer (KYC) regulations is crucial in the realm of tokenization. AML regulations aim to block the integration of illicit funds into the financial system, while KYC regulations center on customer identity verification to prevent money laundering and terrorist financing activities. Complying with these guidelines allows businesses to reduce financial crime risks, uphold operational integrity, and instill trust among stakeholders.
What is KYC?
KYC is a requirement by which regulated entities must obtain personal information about a customer to ensure that their services are not misused and ensure that people applying for financial services are not on sanctions or PEP lists.
What is AML?
AML is a framework of laws and policies aiming to prevent and identify financial crime, including everything from terrorist financing to money laundering. For most institutions, AML will start with KYC — knowing your customers — and will then continue through monitoring financial activity and reporting suspicious behavior.
Read more here
The importance of AML and KYC regulations in tackling financial crimes
AML and KYC regulations serve as vital tools in combating financial crimes such as money laundering, terrorist financing, and fraud. Money laundering concerns disguising illegal funds’ origins to make them appear legitimate, while terrorist financing entails funding terrorist activities.
Employing comprehensive AML and KYC procedures enables businesses to participate in the prevention, detection, and reporting of suspicious activities. Financial institutions and businesses engaged in tokenization must perform rigorous due diligence on customers, scrutinize transactions for unusual patterns, and inform the relevant authorities of any suspicious activities. Complying with AML and KYC regulations not only aids in thwarting financial crimes but also protects businesses' reputation and fosters a secure and reliable tokenization ecosystem.
Read more about Regulatory Landscape
Applying AML and KYC Compliance Measures to Tokenization
Comprehensive Customer Due Diligence (CDD) Execution
The significance of CDD for validating token holders' identities
- In the tokenization process, customer due diligence (CDD) plays a crucial role in verifying and authenticating token holders' identities.
- CDD assists in confirming customers' true identities, evaluating their risk profiles, and uncovering any potential participation in unlawful activities.
- Thorough CDD helps companies adhere to KYC regulations, reduce the likelihood of money laundering, and improve the overall security of their tokenization platform.
The primary components of CDD, including customer identity verification, risk profile assessment, and transaction activity monitoring
- Customer identity verification: Implement strong identity verification methods to authenticate token holders. This could entail gathering government-issued ID documents, performing biometric verification, or using digital identity solutions.
- Risk profile assessment: Determine each customer's risk by considering factors such as occupation, jurisdiction, transaction history, and funding source. Allocate risk scores or categories to effectively prioritize monitoring efforts.
- Transaction activity monitoring: Create mechanisms to track token transactions in real-time. Employ transaction monitoring systems that can detect suspicious patterns like large transactions, frequent transfers, or interactions with high-risk jurisdictions.
Strengthened Transaction Monitoring
The need for real-time token transaction monitoring to identify suspicious actions
- It is vital to monitor token transactions in real-time to detect and prevent potential money laundering or fraudulent activities.
- Prompt detection and response to suspicious patterns, such as multiple high-value transactions or rapid fund transfers, are made possible by real-time monitoring.
Blockchain analytics tools' role in tracking and analyzing transaction patterns
- Blockchain analytics tools take advantage of blockchain technology's transparency to monitor and examine token transactions.
- These tools allow businesses to trace fund flows, pinpoint addresses connected to suspicious activities, and gain insights into transaction patterns that may signal potential money laundering or other illicit actions.
Establishing Solid AML and KYC Policies and Procedures
The significance of creating well-defined AML and KYC policies specifically designed for tokenization:
- For companies engaged in tokenization, it is vital to establish detailed AML and KYC policies that address tokenized assets' unique features and risks.
- These policies should take into account regulatory requirements, industry best practices, and the specific nature of tokenized transactions to ensure compliance efficacy.
Collaborative Efforts with Regulatory Authorities and Compliance Specialists
By actively collaborating with regulatory authorities, businesses can remain informed about current regulatory progress and foresee any alterations that may affect their AML and KYC compliance obligations due to tokenization.
Collaborating with experienced compliance advisors who have deep knowledge of AML, KYC, and tokenization regulations is critical for creating and executing effective compliance structures for tokenization ventures.
These professionals can offer guidance on crafting strong AML and KYC policies, carrying out risk evaluations, and enforcing industry-standard and regulator-approved compliance processes.
TOP 5 KYC Providers

Fractal offers user onboarding for compliance use cases like KYC and KYB. It covers all kinds of KYC levels all in one price. Projects can also make use of its liveness solution which guarantees unique users for e.g. airdrops or crypto games without ever revealing the identity of the user.
SolidProof is a German-based KYC provider with a simple, efficient, and smooth process that adheres to the highest security standards. In addition, the company’s services are affordable, have no hidden costs, and offer a free audit for every project.
Another popular KYC solution is Identity.com. The project focuses on decentralized identity verification and offers a marketplace and gateway protocol. The company does not trade personal information, which increases security and privacy. The project also focuses on decentralization.
Elliptic is another excellent solution for KYC and compliance needs for traditional financial institutions and crypto and NFT projects. They offer various services, including wallet screening, transaction monitoring, VASP screening, and enhanced due diligence.
Blockpass is famous for its quick, easy signup process and automated KYC solution. Blockpass offers a full-service, comprehensive solution for all onboarding needs – including AML watchlist checks. So if you’re looking for a fast, simple, and easy-to-integrate solution, Blockpass is worth considering.
Conclusion
Complying with Anti-Money Laundering (AML) and Know Your Customer (KYC) regulations is essential in tokenization to combat financial crimes, ensure the integrity of operations, and foster trust within the tokenization ecosystem. By implementing robust AML and KYC compliance measures, businesses involved in tokenization can mitigate the risks of money laundering, terrorist financing, and fraud.
The implementation of thorough customer due diligence (CDD), enhanced transaction monitoring, and the development of comprehensive AML and KYC policies tailored to tokenization are vital steps in ensuring compliance. Leveraging technologies such as artificial intelligence (AI) and blockchain analytics tools enhances the efficiency and accuracy of compliance efforts.
Are you interested in tokenization? Contact us!
Start fundraising for your project with Nextrope Launchpad Platform
 en
en  pl
pl