Most MiCA guides tell you to hire a lawyer. That’s necessary but insufficient. The regulation imposes concrete technical requirements that your engineering team must implement: machine-readable white papers in iXBRL format, on-chain transfer restriction logic, reserve verification systems, structured data reporting in ESMA-specified JSON schemas, and operational resilience infrastructure mandated by DORA.
With transitional periods expiring across EU member states by July 2026 and over 53 CASP licenses already granted, the window for building compliant infrastructure is closing. This checklist translates MiCA’s regulatory language into engineering tasks organized by priority, mapped to specific regulation articles, and structured around the architecture decisions that tokenization platform teams face right now.
1. Token Classification Determines Your Architecture
Before writing a single line of smart contract code, your team needs a definitive answer on token classification. MiCA defines three categories, and each one carries fundamentally different engineering requirements.
Asset-Referenced Tokens (ARTs) stabilize value against a basket of assets – currencies, commodities, or other crypto-assets. If your platform tokenizes real estate backed by mixed collateral, or issues tokens pegged to a commodity index, you are likely in ART territory. Engineering implications are severe: you need reserve management smart contracts with segregated custody, quarterly audit hooks, redemption mechanisms, and critically – logic that prevents any form of interest accrual (Article 40). That last point is a trap. Any time-based benefit to holders, including staking rewards, net compensation, or discounts correlated with holding duration, violates MiCA. Your smart contracts must be architected to make this structurally impossible.
E-Money Tokens (EMTs) are pegged 1:1 to a single fiat currency. If you issue a EUR-backed stablecoin, you are building an EMT. The engineering burden here centers on redemption: token holders must be able to redeem at par value at any time. Your contracts need atomic redemption flows, real-time reserve verification, and integration with authorized credit institutions for fiat settlement.
Other crypto-assets (utility tokens, governance tokens) face lighter technical requirements, primarily white paper publication and the 14-day withdrawal mechanism for retail holders. But do not underestimate the white paper’s technical formatting requirements
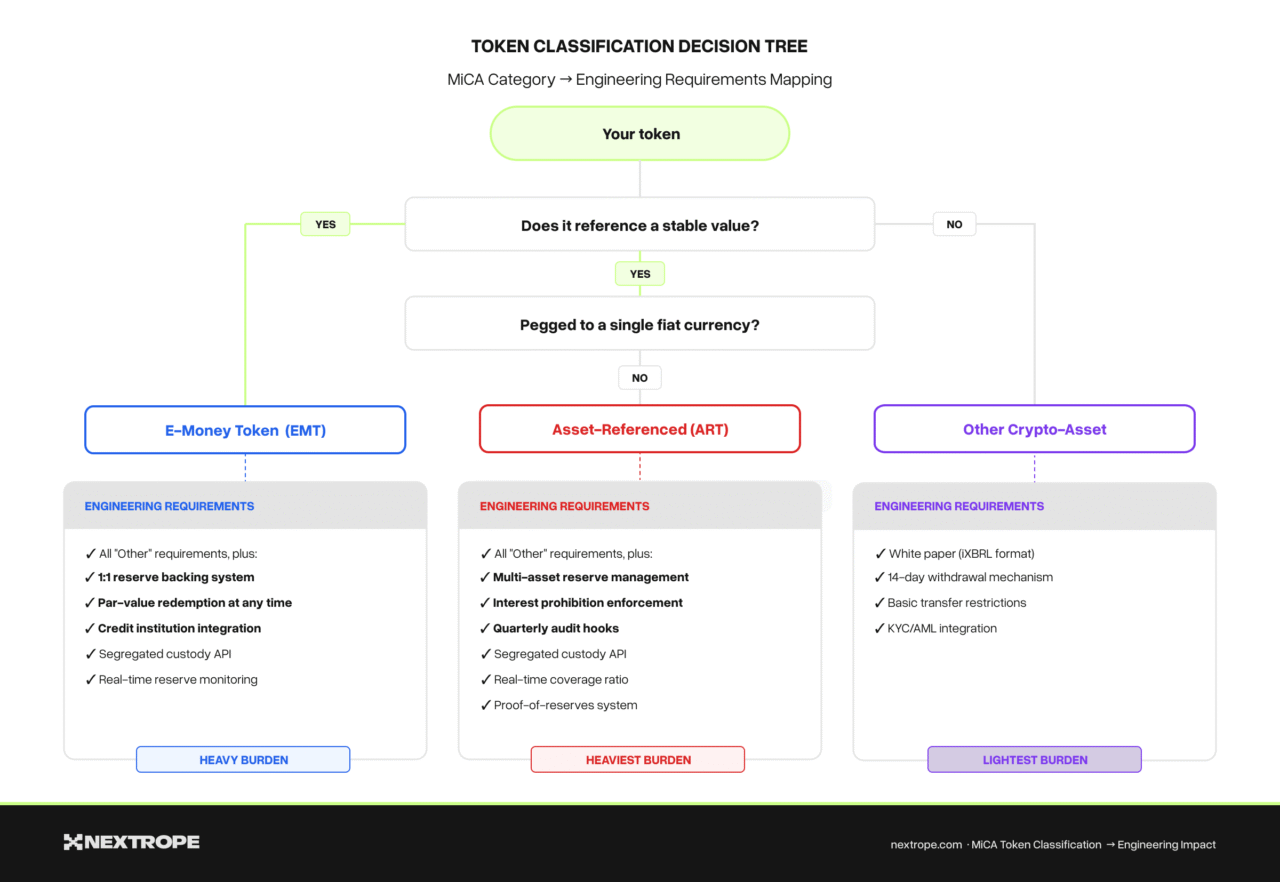
The classification decision cascades through your entire stack. If you are building a tokenization platform that supports multiple token types, your architecture must be modular enough to apply the correct compliance layer per token category. This is where standards like ERC-3643 (with its built-in identity and compliance registries) or ERC-1400 (with its partition-based transfer restrictions) become architectural choices, not just token standard preferences. For a detailed comparison of these standards under MiCA, see our ERC-3643 vs ERC-1400 analysis.
Engineering deliverable: A token classification module that maps each issued token to its MiCA category and automatically applies the corresponding compliance ruleset – reserve requirements, transfer restrictions, withdrawal rights, and reporting obligations.
2. Smart Contract Compliance Layer
MiCA does not prescribe specific smart contract architectures, but its requirements create a clear set of constraints that your contracts must enforce on-chain. Here is what needs to be implemented.
Transfer Restrictions and Identity Binding
Every token transfer on a MiCA-compliant platform must pass through a compliance check. At minimum, this means:
- Whitelist enforcement. Only verified (KYC’d) addresses can hold and transfer tokens. This requires an on-chain identity registry – a mapping of addresses to verified identity claims. ERC-3643’s ONCHAINID framework or a custom ClaimRegistry contract can serve this purpose.
- Jurisdictional checks. MiCA is an EU regulation, but your platform may serve global users. Transfer logic must verify that both sender and receiver are eligible under the token’s jurisdictional rules and the relevant NCA requirements.
- Transfer freeze capabilities. Competent authorities can order asset freezes. Your contracts need an admin-controlled pause mechanism scoped to individual addresses or token-wide, with proper access control (multi-sig or timelock).
14-Day Withdrawal Right (Retail Holders)
For tokens sold directly by the issuer (not yet admitted to trading), retail holders have an unconditional 14-day withdrawal right. Engineering this correctly requires:
- A purchase timestamp registry tracking when each retail holder acquired tokens directly from the issuer.
- A withdrawal function callable within the 14-day window that returns the full purchase amount with zero fees.
- Logic that distinguishes between primary issuance purchases (withdrawal right applies) and secondary market purchases (withdrawal right does not apply).
This is non-trivial if your platform supports both primary and secondary markets. You need clean separation between issuance and trading flows.
Interest Prohibition Logic (ARTs)
Article 40 prohibits any remuneration linked to holding duration for ARTs. If your platform implements staking, yield, or any time-weighted benefit, your smart contracts must structurally exclude ART-classified tokens from these mechanisms. A shared staking contract that accepts any ERC-20 is a compliance violation waiting to happen. Implement token-type checks at the contract level, not just at the frontend.
Engineering deliverable: A compliance middleware contract (or module within your token contract) that enforces transfer restrictions, withdrawal rights, and category-specific rules. This should be upgradeable. MiCA’s Level 2 technical standards are still being refined by ESMA.
3. White Paper: Machine-Readable Format Requirements
The MiCA white paper is not a PDF you upload to your website. As of December 2025, ESMA requires white papers to be published in iXBRL (inline eXtensible Business Reporting Language) format – the same machine-readable standard used for financial reporting under ESEF.
This is a concrete engineering task that most teams underestimate. Here is what is involved:
- XBRL taxonomy compliance. ESMA published the MiCA-specific XBRL taxonomy in August 2025. Your white paper data must map to this taxonomy’s elements. This means structuring token metadata, issuer information, risk disclosures, and rights descriptions as tagged data fields, not free-form text.
- iXBRL rendering. The white paper must be human-readable (rendered as HTML) while simultaneously containing machine-readable XBRL tags. This requires either a specialized iXBRL authoring tool or a custom pipeline that takes structured data and generates compliant iXBRL output.
- ESMA registry integration. White papers are notified to the competent authority and then communicated to ESMA for inclusion in their public register. Your platform should automate as much of this pipeline as possible — generating compliant files, validating them against the taxonomy, and preparing the notification package.
ESMA has published Excel-based examples for each token type to demonstrate the expected format. These are available on the ESMA MiCA webpage and serve as a practical reference for your implementation.
Engineering deliverable: A white paper generation pipeline that takes structured token and issuer data as input and produces validated iXBRL output conforming to ESMA’s taxonomy. If your platform serves multiple issuers, this becomes a self-service tool – a significant product differentiator.
4. Reserve Management Architecture (ARTs and EMTs)
If your platform issues or manages asset-referenced tokens or e-money tokens, reserve management is the most architecturally complex compliance requirement.
Reserve Composition and Segregation
ART issuers must maintain reserves equal to 100% of outstanding tokens, held in segregated accounts with authorized custodians. For your engineering team, this means:
- Segregated custody integration. Your platform must connect to one or more MiCA-authorized custodians via API. Reserve assets cannot be commingled with operational funds.
- Real-time reserve tracking. Build a reserve monitoring service that continuously tracks the value of reserve assets against outstanding token supply. Any shortfall must trigger alerts and potentially pause new issuance.
- Multi-asset reserve composition. ART reserves can include multiple asset types. Your system needs a valuation engine that prices heterogeneous reserve assets and aggregates them into a single coverage ratio.
Proof of Reserves
While MiCA does not mandate on-chain proof of reserves, implementing one is both a competitive advantage and a practical compliance tool. A Merkle-tree-based proof of reserves system allows:
- Third-party auditors to verify reserve coverage without accessing the full reserve database.
- Token holders to independently verify that their holdings are backed.
- Automated quarterly reporting (MiCA requires regular reserve audits by EBA-approved firms).
Redemption Mechanics
EMT holders can redeem at par value at any time. ART holders have redemption rights as specified in the white paper. Your contracts must implement:
- A redemption function that burns tokens and triggers fiat (or reserve asset) settlement.
- Liquidity management logic that ensures sufficient liquid reserves for redemption requests.
- Settlement integration with credit institutions for fiat payouts.
Engineering deliverable: A reserve management module with custodian API integration, real-time coverage monitoring, proof-of-reserves generation, and redemption settlement flows.
5. DORA: Operational Resilience Requirements
MiCA-regulated entities are also subject to the Digital Operational Resilience Act (DORA), which became enforceable in January 2025. DORA is not optional. It applies to all CASPs and token issuers. For your infrastructure team, DORA adds these requirements:
ICT Risk Management Framework
Your platform must implement and document a comprehensive ICT risk management framework covering:
- Asset inventory of all ICT systems, dependencies, and data flows.
- Risk assessment methodology with regular reviews.
- Incident detection, classification, and response procedures.
- Business continuity and disaster recovery plans with tested failover.
Penetration Testing
DORA mandates regular digital operational resilience testing (Articles 24-27). For tokenization platforms, this means:
- Annual penetration testing of all externally facing systems.
- Threat-led penetration testing (TLPT) for significant entities – simulating real attacker scenarios against your smart contracts, APIs, and infrastructure.
- Smart contract audits as part of the security testing scope. While DORA does not explicitly require smart contract audits, regulators increasingly expect them as part of operational resilience evidence.
Third-Party Risk Management
If your platform relies on external services like oracle providers, custodians, blockchain nodes, cloud infrastructure, DORA requires documented oversight of these critical third-party providers, including:
- Contractual provisions for audit rights and incident notification.
- Exit strategies for each critical provider.
- Concentration risk assessment (e.g., dependency on a single cloud provider or oracle).
Incident Reporting
Major ICT-related incidents must be reported to your competent authority. Build automated incident detection and classification that can generate reports in the format your NCA expects.
Engineering deliverable: An operational resilience framework covering ICT risk management, testing schedules, third-party oversight documentation, and incident reporting pipelines. This is infrastructure and process, not just code.
6. AML and Travel Rule Integration
The Transfer of Funds Regulation (TFR) “Travel Rule” applies to all crypto-asset transfers processed by MiCA-regulated entities. Every transfer must include originator and beneficiary information.
On-Chain Identity Binding
Your platform needs a mechanism to associate on-chain addresses with verified identity data. This does not mean putting PII on-chain, rather, it means maintaining an off-chain identity database linked to on-chain addresses through:
- A claim registry (on-chain mapping of addresses to identity attestation hashes).
- Integration with a KYC/KYB provider for identity verification.
- A Travel Rule compliance protocol (such as TRISA, Shyft, or Notabene) for inter-VASP information exchange.
Transaction Monitoring
Beyond identity, your platform must implement real-time transaction monitoring for:
- Sanctions screening against EU and international sanctions lists.
- Suspicious transaction pattern detection (structuring, rapid movement, mixing service interaction).
- Automated SAR (Suspicious Activity Report) generation for your compliance team.
Engineering deliverable: Identity binding infrastructure (claim registry + KYC integration), Travel Rule protocol integration, and transaction monitoring pipeline with automated alerting.
7. Data Standards and Regulatory Reporting
MiCA introduces specific data format requirements that your platform must support.
Order Book Record Keeping
If your platform operates a trading facility, ESMA mandates that order book records be kept in a standardized, machine-readable JSON schema. ESMA has published the exact JSON schema specifications – your trading engine must log all orders and trades in this format, enabling consistent reporting and data exchange with competent authorities.
White Paper Registry
Your platform must maintain a registry of all published white papers and ensure they remain accessible and up-to-date. Any material changes require updated white paper publication and NCA notification within the prescribed timeline.
Ongoing Disclosure
ART and EMT issuers must publish regular transparency reports including reserve composition, redemption statistics, and audit results. Build automated report generation tied to your reserve management and trading systems.
Engineering deliverable: Data pipeline producing ESMA-compliant JSON for order books, automated white paper lifecycle management, and periodic disclosure report generation.
8. Implementation Priority Matrix
With the July 2026 EU-wide deadline as the hard boundary, here is how to sequence implementation:
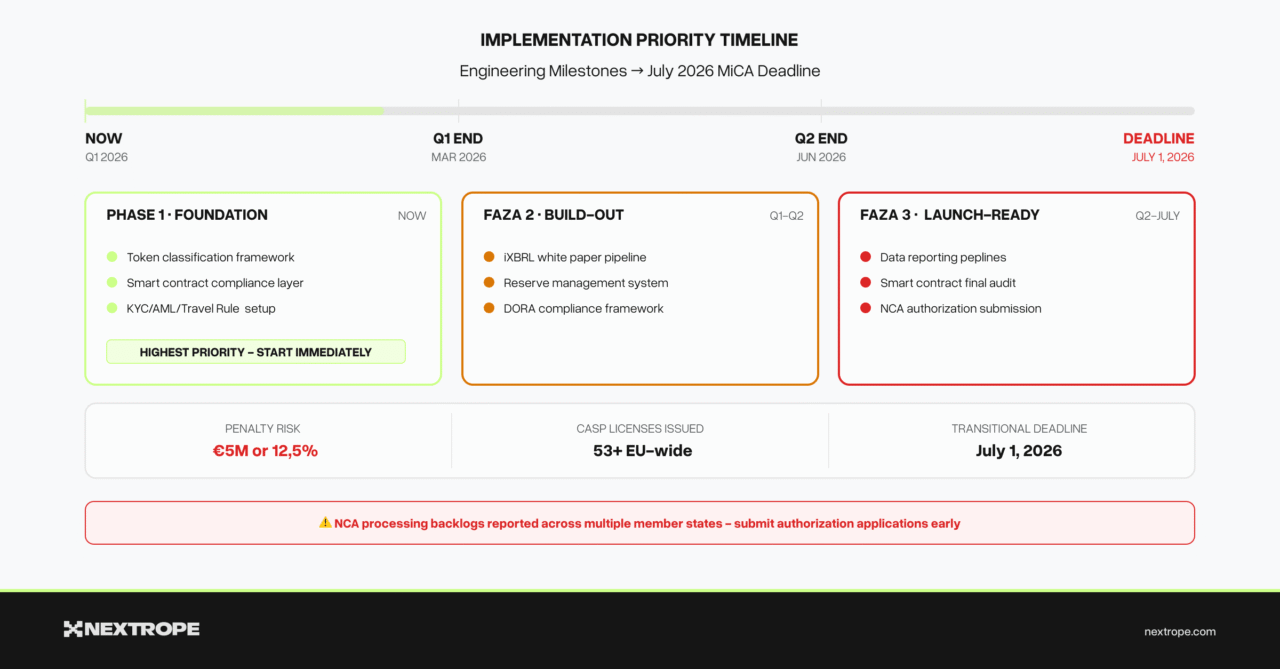
Immediate (Now Q1 2026)
- Token classification framework – define which MiCA category each token falls under. Every subsequent decision depends on this.
- Smart contract compliance layer – transfer restrictions, whitelist enforcement, withdrawal rights. This is your foundation.
- KYC/AML integration – Travel Rule compliance cannot be bolted on later. Build it into your identity infrastructure from day one.
Near-Term (Q1-Q2 2026)
- White paper iXBRL pipeline – ESMA’s formatting requirements are live. Build or integrate tooling now to avoid manual conversion bottlenecks at launch.
- Reserve management system (if issuing ARTs/EMTs) – custodian integration, coverage monitoring, redemption flows.
- DORA compliance infrastructure – ICT risk framework documentation, penetration testing schedule, third-party risk assessments.
Pre-Launch (Q2 – July 2026)
- Data reporting pipelines – ESMA JSON schemas for order books, periodic disclosure automation.
- Incident reporting system – automated detection and NCA-formatted report generation.
- Smart contract audit – final security audit covering all compliance logic. This is both a DORA requirement and a practical necessity.
- NCA engagement – submit your authorization application well before the deadline. National authorities are already reporting processing backlogs.
9. The Compliance Stack: Putting It All Together
A MiCA-compliant tokenization platform is not a monolithic application. It is a stack of specialized components, each addressing a specific regulatory requirement:
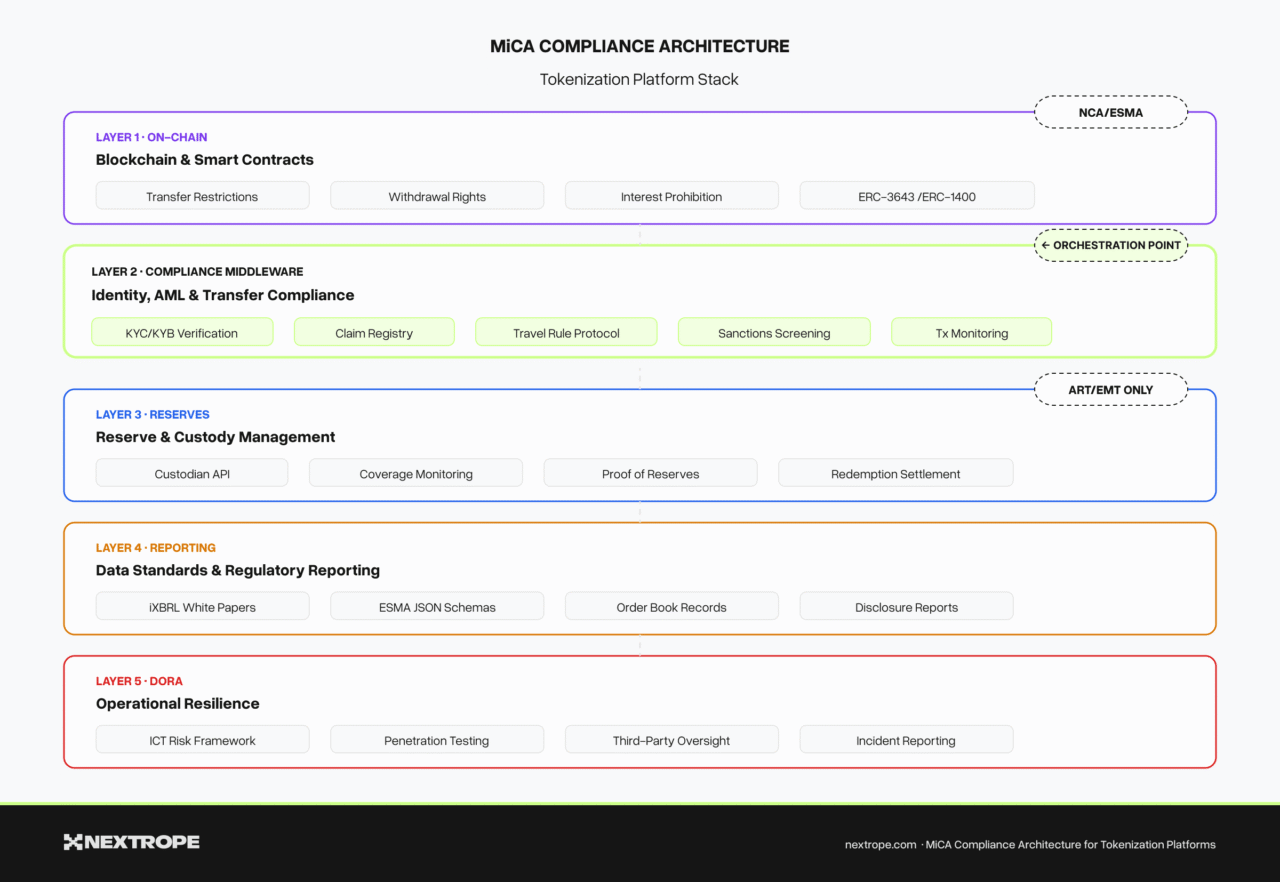
Layer 1: Blockchain & Smart Contracts – Token contracts with built-in compliance hooks (transfer restrictions, withdrawal rights, interest prohibition). Standards like ERC-3643 or ERC-1400 provide a head start, but custom logic is always needed.
Layer 2: Identity & Compliance Middleware – Off-chain identity verification (KYC/KYB), on-chain claim registry, Travel Rule protocol integration, sanctions screening, and transaction monitoring.
Layer 3: Reserve & Custody – Custodian API integration, real-time reserve tracking, proof-of-reserves generation, redemption settlement. Relevant only for ART/EMT issuers.
Layer 4: Data & Reporting – iXBRL white paper generation, ESMA JSON order book logging, periodic disclosure reports, incident reporting pipeline.
Layer 5: Operational Resilience (DORA) – ICT risk management framework, penetration testing program, third-party oversight, business continuity systems.
Each layer can be built independently, but they must integrate cleanly. The compliance middleware (Layer 2) is the orchestration point. It mediates between on-chain token logic and off-chain regulatory requirements.
What This Means for Your Platform
MiCA compliance is not a checkbox exercise – it is an architectural decision that shapes your entire platform. The teams that treat compliance as a first-class engineering concern, rather than a legal afterthought, will ship faster and with fewer costly rewrites.
The technical requirements are concrete and implementable. iXBRL white papers have a published taxonomy. JSON schemas for order books are specified. Transfer restriction patterns are well-understood in standards like ERC-3643. Reserve verification systems have proven architectures. None of this requires inventing new technology – it requires disciplined implementation of known patterns within the regulatory framework.
If your team is building a tokenization platform targeting EU markets, the engineering work starts now. The July 2026 deadline is not a launch date. It is the point after which operating without full compliance carries fines of up to €5 million or 12.5% of annual turnover, potential license revocation, and personal liability for executives.
Nextrope builds MiCA-compliant tokenization platforms for financial institutions across Europe. From smart contract architecture and compliance middleware to reserve management systems, our engineering team has delivered institutional-grade blockchain infrastructure for clients including Alior Bank and SOIL. Contact us to discuss your tokenization platform requirements.