The term "network effects" frequently surfaces as a factor underpinning the exponential growth of cryptocurrencies. But what exactly are network effects in crypto projects, and why are they so important? At its core, a network effect occurs when a product or service becomes more valuable as more people use it. This phenomenon is not exclusive to the digital age; it has influenced the adoption and success of technologies ranging from the telephone to the internet. However, in the context of cryptocurrency, network effects not only fuel adoption but are also directly correlated with market capitalization. This article delves into the mechanics of network effects in crypto and discusses just how much adoption influences projects’ value.
Measuring Network Effects in Crypto
One of the most widely recognized methods for measuring these effects is Metcalfe’s Law, which posits that the value of a network is proportional to the square of the number of its users. Studies have found that this law applies to blockchain networks particularly well. In practice, we measure user base (N) as the number of nodes or active addresses.
Case Studies: Bitcoin and Ethereum
To illustrate the practical application of Metcalfe’s Law in cryptocurrencies, let's examine Bitcoin and Ethereum, two of the most prominent blockchain networks.
- Bitcoin: As the first cryptocurrency, Bitcoin has demonstrated a remarkable correlation between its network size and value. Historical data shows that periods of rapid growth in the number of active wallets are closely followed by increases in Bitcoin's market price. Pearson’s correlation coefficient between BTC price and a squared number of nodes is approximately 0.9. In the case of squared number of active addresses, it’s approximately 0.95. This pattern underscores just how important network effects are.
- Ethereum: Ethereum's utility extends beyond mere financial transactions, encompassing smart contracts and decentralized applications (DApps). This added functionality attracts a diverse user base, further amplifying its network effects. Pearson’s correlation coefficient takes similar values as in BTC case.
Network Effects and Cryptocurrency Adoption
The adoption of cryptocurrency is significantly influenced by network effects, which not only enhance the value of the digital currency but also contribute to its widespread acceptance and use. As the network of users grows, the cryptocurrency becomes more useful and desirable, creating a virtuous cycle that attracts even more users. This is particularly evident in the context of payments and remittances, where the value of a cryptocurrency network increases with the number of individuals and institutions willing to accept and transact in the currency.
Enhancing Security and Trust
One of the critical ways network effects contribute to cryptocurrency adoption is by enhancing the security and trustworthiness of the network. Blockchain technology, the foundation of most cryptocurrencies, becomes more secure as more participants join the network. The decentralized nature of blockchain makes it increasingly difficult for malicious actors to compromise the network's integrity, thereby bolstering user confidence in the system. This enhanced security is a direct consequence of the network effects, as a larger network provides greater resistance against attacks.
Impact on Liquidity and Market Depth
A larger user base means more transactions and, consequently, greater liquidity, making it easier for users to buy and sell without causing significant price fluctuations. This increased market depth attracts investors and traders, further fueling cryptocurrency adoption. That’s especially important for Dapps which release native tokens traded on DEXs like Uniswap. It’s common for teams to provide initial liquidity that fosters trading, but it’s much better when that liquidity is provided by users.
Fostering network effects techniques
Very strong correlation between the value of blockchain projects and their user base makes it clear that adoption is very important. So, how should projects foster the growth of their user base?
Airdrops
Airdrops are a very common (and relatively cheap) way to grow user base of a network in its beginnings. The way they work is the following: projects allocate a certain number of tokens (e.g. 1% of total supply) to people who engage with the project. For example, a project may announce that people who retweet and like their posts on X a certain number of times will get some tokens. Another type of engagement might be participating in testnet and providing feedback to founders. Airdrops are effective because even if only 5% of these attracted users will stay for long-term then it’s still a great return on investment.
Subsidized incentives
When the project is just starting it may be a good idea to allocate some capital towards higher incentives for early users. An example might be providing higher APY for stakers (like 10%, instead of 5%) for the first 6 months. While such subsidized incentives are good in the beginning they must end at some point. That’s because they’re unsustainable in the long term. An example of what can happen if unsustainable incentives last for a little too long is the Anchor Protocol’s case. Anchor hoped to attract a lot of users by providing 15% APY. In that sense it achieved success, but because it didn’t end the program in time, the protocol became unsolvable and crashed. Though while it lasted the network’s growth was truly exponential.
Vision Oriented Project
Probably the most sustainable and organic way to grow your user base is by showing users an inspiring vision associated with your project. This is about creating a protocol that in some way promises to change the world for the better. An example may be Cardano which acquired an enormous fanbase oriented around its mission statement. That was despite poor user experience in their beginnings.
Challenges and Limitations
Despite the positive impact of network effects on cryptocurrency adoption and value, some notable challenges and limitations must be acknowledged.
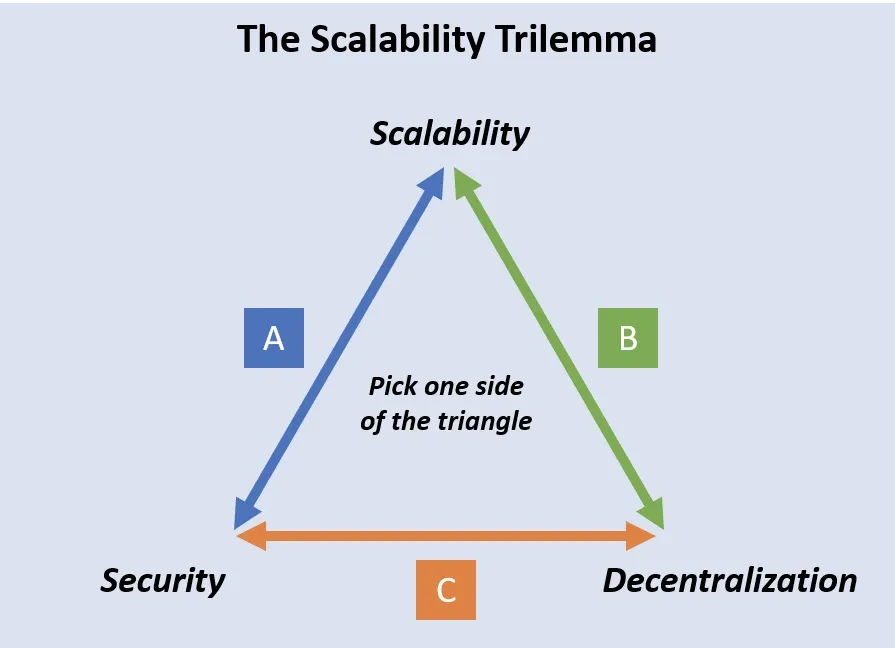
Scalability Concerns
A primary challenge posed by network effects is scalability. As the network grows, the underlying blockchain technology must be able to handle an increasing number of transactions quickly and efficiently. However, many cryptocurrencies, including Bitcoin and Ethereum, have encountered difficulties scaling their networks to meet demand without compromising security or decentralization. This is the most important factor hindering adoption, since many users prefer to use a centralized payment system, just because it’s more efficient. For example, VISA can process 24k TPS, while BTC can process 7 TPS.
Conclusion
While network effects are a powerful driver of cryptocurrency adoption and value, they also present significant scalability challenges that must be addressed. However, in the case of emerging projects, benefits coming from increased adoption outweigh the costs and it’s shown that the greatest factor influencing the value of these projects is their user base.
If you're looking for ways to foster the adoption of your DeFi project, please reach out to contact@nextrope.com. Our team is ready to help you create a strategy that will grow your user base and ensure long-term growth.
FAQ
What are network effects?
- Network effects is a term describing a situation when the value of a network grows more than proportionally relative to the number of users.
How do network effects influence projects' value?
- There is a very strong correlation between a squared number of active addresses/nodes and the market capitalization of projects.
How to foster adoption and occurrence of network effects within my project?
- By building a community. This can be achieved through orienting protocol around an inspiring vision, airdrops, and subsidized incentives for users.
 en
en  pl
pl