As the importance of security and trust have grown within the blockchain technology sphere, it has become vital to establish strong methods for safeguarding sensitive information and maintaining privacy. Zero-knowledge proof, a mechanism that has attracted considerable interest, allows for the verification of data without exposing the actual content. In this article, we will delve into the effective incorporation of zero-knowledge proof within blockchain applications. We will explain how to implement Zero-Knowledge Proof in Blockchain Application. By comprehending its underlying principles and complexities and adhering to the steps detailed below, businesses can utilize this influential instrument to enhance their blockchain solutions in terms of privacy, integrity, and authentication.
Understanding Zero-Knowledge Proof
Fundamentally, zero-knowledge proof is a cryptographic notion permitting one entity, termed as the prover, to demonstrate the accuracy of a certain claim to another entity, called the verifier, without disclosing any details about the claim itself. Put simply, zero-knowledge proof allows the prover to persuade the verifier of a statement's truth while keeping the relevant data or knowledge hidden. This concept was first put forward by Shafi Goldwasser, Silvio Micali, and Charles Rackoff in 1985 and has since emerged as an indispensable resource in maintaining data privacy and security.
For a zero-knowledge proof to be successful, it requires four main elements. The prover, the verifier, the statement, and the proof. The prover is responsible for establishing the truthfulness of a statement without divulging any actual information. On the other hand, it is up to verifier to confirm that proof offered by prover is accurate without acquiring any knowledge concerning underlying details. Meanwhile, the statement symbolizes what the prover seeks to validate whereas proof embodies evidence supplied by prover in order to persuade verifier regarding validity of said statement.
Why Use Zero-Knowledge Proof in Blockchain?
The blockchain technology, characterized by its decentralized nature, transparency, and immutability, has revolutionized various sectors. However, as much as transparency is a boon in blockchain applications, it can sometimes become a bane when it comes to privacy. This is where the concept of Zero-Knowledge Proof (ZKP) comes into play.
Benefits of Zero-Knowledge Proof in Blockchain
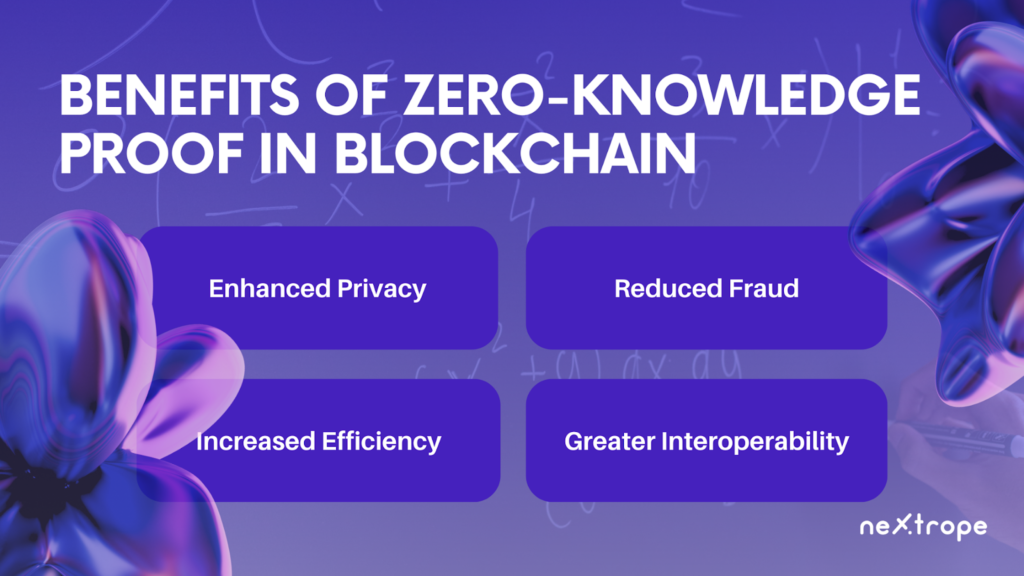
Zero-Knowledge Proofs offer several advantages that make them an attractive choice for enhancing privacy and security in blockchain applications:
- Enhanced Privacy: ZKP allows users to verify transactions without revealing any additional information beyond the fact that the transaction is valid. This helps protect sensitive information from being publicly accessible on the blockchain.
- Reduced Fraud: By ensuring that only valid transactions are added to the blockchain, ZKPs can significantly decrease the potential for fraudulent activity.
- Increased Efficiency: In some scenarios, ZKP can reduce the amount of data that needs to be stored on the blockchain. With ZKP, the proof of a transaction's validity can be much smaller than the transaction data itself.
- Greater Interoperability: ZKP enables secure interactions between different blockchain systems, facilitating cross-chain transactions and increasing the overall interoperability of the blockchain ecosystem.
Current Applications of Zero-Knowledge Proof in Blockchain
There are several notable applications currently using Zero-Knowledge Proofs to enhance their operations:
- Zcash: This cryptocurrency uses ZKP (specifically a variant called zk-SNARKs) to provide its users with the option to hide the sender, receiver, and value of transactions, all while allowing network miners to verify transactions without gaining any knowledge about the specifics.
- Ethereum: Ethereum has been exploring the integration of ZKP to improve both privacy and scalability. It aims to enable private transactions and to create off-chain transactions that can be verified on-chain.
- StarkWare: StarkWare uses ZKP (specifically zk-STARKs) to enhance scalability and privacy in various applications, including decentralized exchanges and gaming platforms. The technology enables processing and verification of large amounts of data off-chain, reducing the load on the blockchain itself.
These examples illustrate the diverse uses and potential of Zero-Knowledge Proofs in blockchain applications. The ability to prove and verify transactions without revealing any additional information is a powerful tool that can significantly enhance the privacy, security, and efficiency of blockchain systems.
How to Implement Zero-Knowledge Proof in blockchain applications
The initial step involves a comprehensive grasp of ZKP and its variants such as zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) and zk-STARKs (Zero-Knowledge Scalable Transparent ARguments of Knowledge). This involves studying cryptographic principles, mathematical concepts, and computational theories underpinning these proofs.
Read our Ultimate Guide to ZKP: zk-SNARKs vs zk-STARKs
The next phase of 'How to Implement Zero-Knowledge Proof' requires understanding the blockchain platform. This includes knowledge of the platform's architecture, its scripting language, and its privacy and security protocols. The choice of platform may depend on the specific requirements of the application, as different platforms offer varying degrees of support for ZKP.
The actual implementation process begins with defining the private and public inputs for the proof. The private inputs are the data that the prover wants to keep secret. The public inputs are the information that can be openly shared. A 'witness' is then generated, which is a solution to the mathematical problem defined by these inputs.
The next step is the creation of a proving key and a verification key, using a setup algorithm. The proving key generates proofs, and the verification key checks the validity of these proofs. After this, the prover uses the proving key and the witness to create a proof. It asserts that they know a solution to the problem without revealing the solution itself.
Once the proof is generated, it can be verified by anyone using the verification key. This ensures that the proof is valid and that the prover knows the private inputs. All without revealing any additional information.
After the successful verification of the proof, it can be integrated into the blockchain application. This could involve creating transactions that include the proof, or setting up smart contracts that require a valid proof to execute certain functions.
Challenges and Considerations
Incorporating zero-knowledge proof into blockchain applications entails numerous hurdles and deliberations. To capitalize on the advantages of zero-knowledge proof, grasping and alleviating these challenges is vital. Some important aspects to take into account are:
Operational Overhead and Proficiency
Assessing Performance Consequences: The computations in zero-knowledge proof can be demanding, possibly impacting blockchain applications' performance. It is critical to examine the operational overhead induced by the chosen protocol and refine it as much as feasible.
Refinement Approaches: Investigating methods like enhanced algorithms, parallel computation, or assigning calculations to specialized equipment can help alleviate operational overhead and boost efficiency.
Expandability and Compatibility
Tackling Expandability Issues: Zero-knowledge proof protocols might cause challenges in expandability when employed on a massive scale. As the blockchain network expands, both computational necessities and communication intricacies of zero-knowledge proofs can considerably rise. Inspecting expandability solutions, like sharding or layer-two protocols, assists in surmounting these issues.
Compatibility Among Networks: Certifying harmony and compatibility of implementations amidst various blockchain networks is essential for unobstructed collaboration between diverse systems. Contemplate standards and protocols that enable cross-chain interaction to accomplish compatibility.
Security Threats and Confidence Presumptions
Scrutinizing Assumptions and Vulnerabilities. ZKP protocols are founded on distinct assumptions and cryptographic building blocks. Evaluating assumed premises and possible susceptibilities tied to the chosen protocol is imperative. Staying up-to-date with any breakthroughs or latent flaws in the protocol aids in maintaining long-term security.
Supplementary Security Precautions. Although zero-knowledge proofs deliver superior privacy and security, one should not be overly dependent on them. Implementing supplementary safety measures, like secure key administration, encryption, and stringent access control, offers extra levels of safeguarding.
Thorough contemplation of these hurdles and addressing them throughout the implementation stage enables organizations to surmount potential impediments and effectively integrate zero-knowledge proof into their blockchain applications. It is critical to stay current with the newest research and developments in zero-knowledge proof methods to warrant the security, efficacy, and expandability of the executed solution.
 en
en  pl
pl