In the ever-evolving world of blockchain, artificial intelligence (AI), and cryptocurrencies, bounty programs have emerged as a popular strategy for incentivizing participants. This article explores the concept of bounty programs and their relevance in 2023, shedding light on their origins, purpose, and key considerations for companies utilizing them in the cryptocurrency industry.
Understanding Bounty Programs
Bounty programs play a significant role in the world of cryptocurrencies and blockchain. These programs are designed to incentivize a wide range of participants involved in an initial coin offering (ICO) to contribute to its success. In order to fully grasp the concept of bounty programs, it is crucial to delve into their definition, background, and key takeaways.
Definition and Background

Bounty programs are incentives offered to participants involved in an ICO.
- ICOs are the cryptocurrency industry's equivalent of initial public offerings (IPOs) in traditional finance.
- The origins of bounty programs can be traced back to the digital video gaming world, where rewards were given to gamers who identified bugs in games.
Key Takeaways
- Bounty programs are used to incentivize developers and marketers before and after an ICO.
- Participants in bounty programs can receive cash rewards or tokens that can be redeemed later.
- Bounty programs operate in a legal gray area, often walking a fine line between marketing and potential fraud.
- The Securities and Exchange Commission (SEC) has used ICO bounty programs as evidence of criminal activity.
Understanding the fundamentals of bounty programs is crucial for individuals and companies operating in the cryptocurrency space. These programs serve as a mechanism to engage participants and promote ICOs, but it is essential to navigate the legal and ethical considerations associated with their implementation.
Post-ICO Bounty Programs
After the completion of an initial coin offering (ICO), bounty programs can continue to play a crucial role in the development and promotion of the blockchain project. Post-ICO bounty programs focus on fine-tuning the released blockchain, addressing bugs, and expanding the project's global reach. Let's explore the key aspects of post-ICO bounty programs.
1. Post-ICO Stage Overview
- The focus shifts from fundraising to refining and optimizing the blockchain project.
- Bounty programs continue to incentivize participants to contribute their skills and expertise.
2. Bug Bounty Programs
- Developers and coders are incentivized to detect and report any flaws or vulnerabilities in the blockchain.
3. Translators and Global Reach
- Post-ICO bounty programs may engage translators to ensure the project's documentation and materials are accessible worldwide.
- These translators help bridge language barriers and contribute to the project's global adoption and expansion.
Post-ICO bounty programs provide ongoing opportunities for developers and other participants to contribute to the project's success. By addressing bugs and facilitating global accessibility, these programs enhance the blockchain's functionality and reach.
Examples of Crypto Bug Bounty Programs in 2023
Boba Network
Currently, the L2 scaling solution Boba is experiencing a series of successes, as numerous projects are employing its hybrid compute solution for multi-chain dApps. On January 13th, they initiated a new bounty program offering a maximum payout of an impressive $1M. The reward distribution is based on the vulnerability's threat level discovered.
To categorize the discovered bugs' severity, Boba is using a five-tier scale, encompassing not only issues affecting the protocol but also those related to smart contracts and apps developed on the platform. With a minimum reward of $50,000 available, skilled developers have strong incentives to meticulously examine Boba and uncover any vulnerabilities they might find.
Balancer
Widely battle-tested and often replicated, the Balancer multi-chain liquidity protocol remains vigilant in identifying threats. Through the Immunefi bounty program, rewards ranging from $50,000 to $1M are offered based on the severity of discovered vulnerabilities.
Medium-level threats don't necessitate a Proof of Concept, but they have a maximum payout limit of 25 ETH. In contrast, high-level threats demand a PoC and come with more significant rewards. The maximum payout for high-severity smart contract vulnerabilities is set at 10% of the economic damage caused.
Dexalot
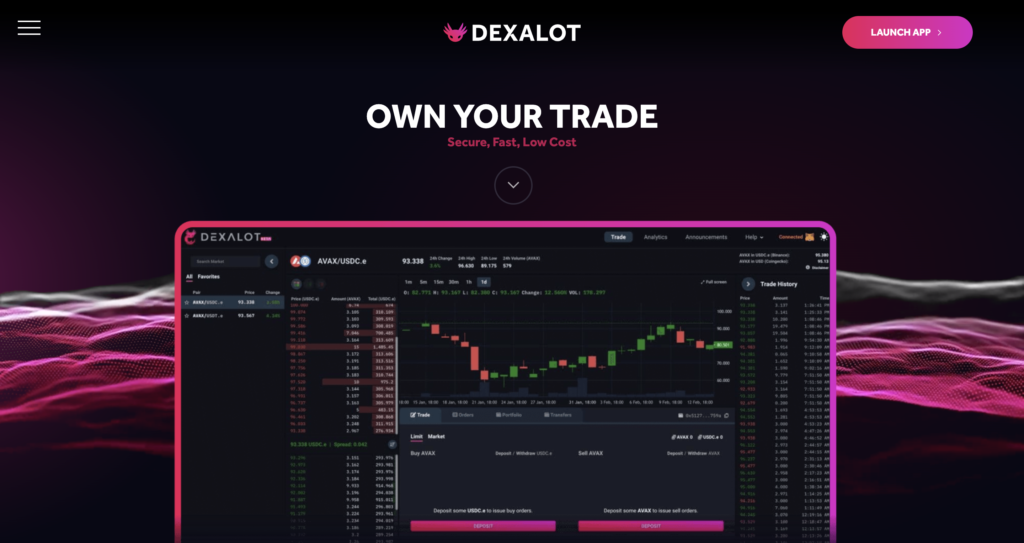
Dexalot, a decentralized exchange built on Avalanche, emulates the appearance and functionality of a centralized exchange, featuring a central limit order book. This allows users to securely and efficiently trade cryptocurrencies without slippage or custody risks. On January 13, Dexalot initiated its bug bounty program, offering rewards of up to $100,000 for each critical bug discovered.
In collaboration with HackenProof, the program will grant rewards ranging from $1,000 for minor vulnerabilities to $100,000 for critical ones. Eligible vulnerabilities include those related to fund theft or loss, unauthorized transactions, and transaction manipulation.
Bug bounties present an excellent opportunity for individuals with technical expertise who enjoy dissecting protocols line by line. Discovering a significant vulnerability could result in a substantial reward. So go ahead and fire up your Github to start downloading those repositories.
Criticism of Bounty Programs
While bounty programs have gained popularity, they have also faced criticism, particularly due to potential unethical practices and regulatory concerns. Understanding the criticisms surrounding bounty programs is essential for companies considering their implementation.

1. Comparison to Pump-and-Dump Schemes
- Some critics draw parallels between ICO bounty programs and pump-and-dump schemes.
- Allegations suggest that participants may engage in disguised promotion while appearing as disinterested parties, potentially misleading investors.
2. Regulatory Concerns and SEC Warning
- The Securities and Exchange Commission (SEC) has raised concerns about fraudulent ICOs utilizing bounty programs.
It is crucial for companies and individuals to exercise caution and ensure ethical practices when implementing bounty programs. Adhering to regulatory guidelines and maintaining transparency can help mitigate potential risks and criticisms associated with these programs.
Conclusion
Bounty programs have become an integral part of the cryptocurrency industry, providing incentives for participants in ICOs and beyond. By understanding the origins, stages, and criticisms surrounding bounty programs, companies can make informed decisions about their implementation.
As the cryptocurrency industry evolves, companies must navigate the fine line between effective marketing strategies and potential legal and ethical risks associated with bounty programs. By adhering to best practices, maintaining transparency, and being mindful of regulatory guidelines, businesses can leverage bounty programs effectively to promote their blockchain, AI, and cryptocurrency projects.
Nextrope Tokenization Launchpad Platform
Nextrope Launchpad Platform is a White Label solution in a Software-as-a-Service model that helps you launch your project within a month and fundraise with Initial Coin Offering (ICO) or Security Token Offering (STO).
 en
en  pl
pl